If I asked you to name the biggest cybersecurity threats in your office, you’d probably say phishing e-mails, malware...
Cybersecurity
The Fake Vacation E-mail That Could Drain Your Bank Account
Planning a vacation this year? Make sure your confirmation e-mail is legit BEFORE you click anything! That’s right,...
The Biggest Mistakes I See Business Owners Making in IT and Cybersecurity
A client recently asked me, “What mistakes do you see business owners making the most when it comes to IT and...
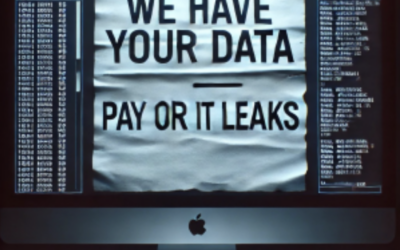
Hackers Might Not Ransom You Anymore – They’ll Just Extort You Instead!
Think ransomware is your worst nightmare? Think again. Hackers have found a new way to hold your business hostage –...




Recent Comments