Remote Monitoring And Management (RMM)
Remote Monitoring and Management (RMM) Service Overview
Our RMM services provide 24/7 System Monitoring to ensure continuous surveillance of your IT infrastructure. Moreover, with the ever-evolving landscape of software, our Patch Management and Software Updates ensure your systems remain up-to-date and secure against the latest vulnerabilities. And in the rare event that something goes amiss, our Real-time Alerts and Automated Response mechanisms jump into action, mitigating risks and ensuring minimal downtime. Dive in to learn how our comprehensive RMM solutions can be the backbone of your business’s tech ecosystem.
Solutions We Offer
Understanding the criticality of keeping systems current, we integrate Patch Management and Software Updates to combat vulnerabilities and maintain software efficiency. But our services go beyond mere monitoring and updates. When potential challenges arise, our Real-time Alerts and Automated Response system is primed to tackle issues head-on, reducing downtime and ensuring business continuity. Trust in our expertise to equip your business with state-of-the-art RMM tools that drive optimal performance and security.
24/7 System Monitoring
Patch Management and Software Updates
Real-time Alerts and Automated Response
Keep Your Systems Secure and Running 24/7
Blog Articles
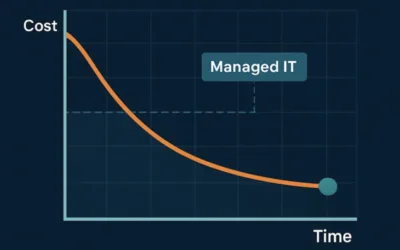
How Managed IT Services Actually Reduce IT Costs Over Time
At first glance, managed IT services can feel like an added expense. In reality, they often reduce total IT costs over time, sometimes significantly. The key difference lies in how problems are handled: prevention versus reaction. Let’s explore how managed IT changes...
7 Signs Your Business Has Outgrown Break-Fix IT Support
For years, many small and mid-sized businesses relied on break-fix IT support: when something breaks, you call for help, pay the bill, and move on. While this approach may seem cost-effective on the surface, it becomes increasingly risky as businesses grow—especially...
What Managed IT Services Really Include (and What They Don’t)
When people hear the term Managed IT Services, they often picture a simple arrangement: something breaks, they call IT, and it gets fixed. While that reactive model may have worked years ago, it’s no longer enough for today’s businesses—especially those in regulated...