Mobile Device Management (MDM)
Mobile Device Management (MDM) Service Overview
Firstly, we emphasize robust Application and Configuration Management to ensure your devices run optimally with tailored software settings. Secondly, our Device Security and Monitoring services provide real-time oversight and proactive defenses against potential threats. Lastly, in the event of unforeseen circumstances or potential data breaches, our Remote Device Wipe and Lock capabilities offer immediate protective measures to prevent unauthorized access. Dive in to learn how our integrated approach can fortify your organization’s mobile infrastructure.
Solutions We Offer
Equally pivotal is our commitment to Device Security and Monitoring, providing businesses with the assurance that every device is monitored in real-time, safeguarded against potential cyber threats, and always operates within the prescribed security parameters. Additionally, understanding the unpredictable nature of the mobile ecosystem, we’ve incorporated Remote Device Wipe and Lock capabilities, a crucial safety net that allows organizations to swiftly respond to potential security breaches or loss scenarios, ensuring that data remains un-compromised. With these tailored solutions, we aim to optimize the efficacy of your mobile operations, minimizing risks and maximizing productivity.
Application and Configuration Management
Device Security and Monitoring
Remote Device Wipe and Lock
Receive Comprehensive Mobile Device Security and Management
Blog Articles
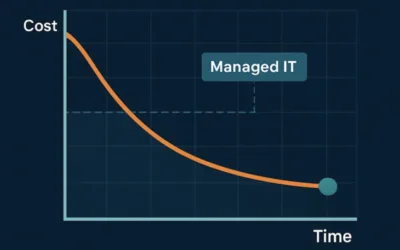
How Managed IT Services Actually Reduce IT Costs Over Time
At first glance, managed IT services can feel like an added expense. In reality, they often reduce total IT costs over time, sometimes significantly. The key difference lies in how problems are handled: prevention versus reaction. Let’s explore how managed IT changes...
7 Signs Your Business Has Outgrown Break-Fix IT Support
For years, many small and mid-sized businesses relied on break-fix IT support: when something breaks, you call for help, pay the bill, and move on. While this approach may seem cost-effective on the surface, it becomes increasingly risky as businesses grow—especially...
What Managed IT Services Really Include (and What They Don’t)
When people hear the term Managed IT Services, they often picture a simple arrangement: something breaks, they call IT, and it gets fixed. While that reactive model may have worked years ago, it’s no longer enough for today’s businesses—especially those in regulated...