Network Management
Network Management Service Overview
Network Design, Installation, and Optimization are fundamental to ensuring that the infrastructure is robust, scalable, and geared for the future. Lastly, with the increasing need for secure remote access, VPN Setup and Maintenance has become indispensable, letting organizations connect confidently and securely, irrespective of geographical boundaries. Dive into these core facets of Network Management and discover how they can elevate your IT strategy to the next level.
Solutions We Offer
Delving deeper, a well-laid Network Design, Installation, and Optimization not only sets the backbone for a resilient IT infrastructure but also prepares businesses to adapt to future technological shifts. Meanwhile, as distributed teams and remote operations become commonplace, the significance of robust VPN Setup and Maintenance can’t be overstated. It’s not just about connectivity; it’s about safeguarding each byte of data and fostering trust. Together, these facets shape a resilient, responsive, and future-ready IT strategy for organizations of all sizes.
Bandwidth and Performance Monitoring
Network Design, Installation, and Optimization
VPN Setup and Maintenance
Navigating modern IT requires a blend of seamless operations and robust security. With our specialized Network Management solutions, we address everything from bandwidth intricacies to secure virtual connections, ensuring businesses are primed to thrive in the digital age.
Strengthen Your Network for the Future!
Ensure your IT infrastructure is secure, efficient, and ready for growth. From Bandwidth Monitoring to VPN Setup and Network Optimization, we provide the solutions you need for a seamless network. Contact us today to elevate your network management strategy and stay ahead in a connected world!
Blog Articles
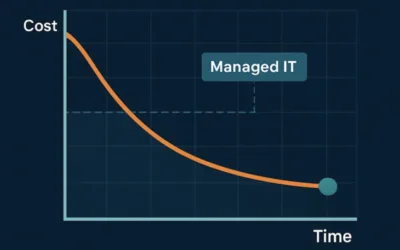
How Managed IT Services Actually Reduce IT Costs Over Time
At first glance, managed IT services can feel like an added expense. In reality, they often reduce total IT costs over time, sometimes significantly. The key difference lies in how problems are handled: prevention versus reaction. Let’s explore how managed IT changes...
7 Signs Your Business Has Outgrown Break-Fix IT Support
For years, many small and mid-sized businesses relied on break-fix IT support: when something breaks, you call for help, pay the bill, and move on. While this approach may seem cost-effective on the surface, it becomes increasingly risky as businesses grow—especially...
What Managed IT Services Really Include (and What They Don’t)
When people hear the term Managed IT Services, they often picture a simple arrangement: something breaks, they call IT, and it gets fixed. While that reactive model may have worked years ago, it’s no longer enough for today’s businesses—especially those in regulated...