IT Strategy And Management

Cloud Services
Empower your business operations with our cutting-edge Cloud Services, offering unparalleled scalability, flexibility, and security, tailored to streamline processes and ensure you remain competitive in today’s rapidly evolving digital landscape.

Hardware and Software Procurement
Streamline your operations with our tailored hardware and software procurement services, sourcing the best-fit technology solutions to empower your business and maximize ROI.

Infrastructure Management
Optimize your IT backbone with our comprehensive infrastructure management services, ensuring reliable performance, scalability, and seamless integration tailored to your business’s unique demands.

IT Consulting and Strategy
Transform your organization’s technological trajectory with our IT consulting and strategy expertise, delivering tailored roadmaps and insights to propel your business into a dynamic digital future.

Network Management
Ensure seamless connectivity and optimal performance with our network management services, leveraging cutting-edge tools and expertise to keep your business connected and secure in a hyper-connected world.
Ready to Transform Your IT Strategy?
Unlock the full potential of your business with our comprehensive IT strategy and management services. From scalable cloud solutions to robust infrastructure management, we provide the expertise and technology you need to stay ahead. Contact us today to begin optimizing your technology and drive lasting success in the digital era.
Link Computer Corporation’s Latest News and Updates
Blog Articles
The Hidden Costs of Downtime (and Why It’s More Expensive Than You Think)
When systems go down, the most obvious cost is lost productivity. But downtime affects far more than just missed work time. Let’s look at the hidden costs many organizations overlook. Hidden Cost #1: Lost Revenue No systems means no transactions, no patient...
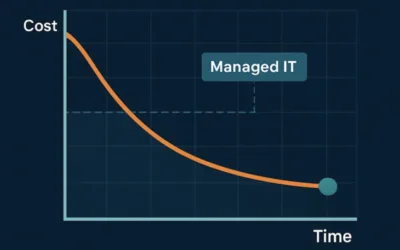
How Managed IT Services Actually Reduce IT Costs Over Time
At first glance, managed IT services can feel like an added expense. In reality, they often reduce total IT costs over time, sometimes significantly. The key difference lies in how problems are handled: prevention versus reaction. Let’s explore how managed IT changes...
7 Signs Your Business Has Outgrown Break-Fix IT Support
For years, many small and mid-sized businesses relied on break-fix IT support: when something breaks, you call for help, pay the bill, and move on. While this approach may seem cost-effective on the surface, it becomes increasingly risky as businesses grow—especially...